How to Remove Mysearch123.com from Chrome, Firefox or IE in several easy steps? Follow the Mysearch123.com removal instructions and you will stop the browser hijacker.
Mysearch123.com is a malevolent and intrusive browser hijacker. This harmful tool causes an entire myriad of troubles once it settles into your system. It slithers its way in quite deceptively through slyness and finesse, and once it’s in, it starts wreaking havoc. As soon as it latches on, issues pile up almost instantaneously. This hazardous infection shouldn’t be underestimated as it can cause you an excessive amount of troubles you can otherwise easily avoid. Oh, yes. All of the damages the tool will force you to endure and deal with on a daily basis can be easily avoided if you just delete the hijacker as soon as it reveals its presence to you. That usually happens shortly after infiltration. You just turn on your PC one day and find your default homepage and search engine replaced with Mysearch123.com. You have no memory approving this reshuffle, or even installing the tool I the first place, but there it is! That’s because after it fools you into installing it, the hijacker is no longer bound to ask your permission for anything else. It can change anything and everything it feels like changing, and you’ll just have to deal with it. You’ll be greeted by daily unauthorized reshuffles, each one more dangerous than the one before. And, the pile of troubles will only grow with each day, so don’t delay deleting the hijacker! If you wish to save yourself a ton of headaches and troubles, be sure to get rid of it as soon as it first reveals its presence. Get rid of Mysearch123.com at once! It’s for the best.
Mysearch123.com is immensely resourceful when it comes to gaining access to your system. The tool is a master in the arts of deceit, and it has no problem tricking you into approving its installation. Even though, the hijacker is bound to seek your approval before it installs itself on your PC that doesn’t slow it down one bit. In fact, you don’t even see it coming your way. The hijacker is so greatly skilled that, it not only fools you into giving it the green light, but also keeps you utterly oblivious to the fact that you did. More often than not, it sneaks in undetected by hitching a ride with spam email attachments, corrupted links or websites, or freeware. It uses them as a shield to hide behind and enters your computer without you having a single clue about it. It can also pose as a false system or program update, like Java or Adobe Flash Player. Do you see the pattern here? All of these methods of invasion the tool uses so often rely on your haste, naivety, and distraction. So, maybe if you don’t provide them, you won’t get stuck with such a hazardous tool. Be more careful and don’t rush! After all, a little extra attention can go a long, long way.
Is this dangerous?
As was already mentioned, once Mysearch123.com gains access to your PC, it’s no longer required to ask for your approval on anything it wishes to do. The tool can perform any and all changes it feels like, and you’ll have to accept them. In fact, it doesn’t even have to inform you. It can simply surprise you! And, imagine your surprise when you turn on your computer one day and find it overwhelmed with malware. Oh, yes. If the hijacker so desires, it can easily install as many malevolent tools as it so wishes. Also, it can reshuffle your settings in a manner that will block you from accessing your favorite websites. It can do anything! The only way, to stop the hijacker from causing you harm, is to delete it at once! You’ll spare yourself an entire array of problems. For example, the hijacker also displays adware’s most unfavorable and infuriating trait. Each time you try to go online, it will flood you with a never-ending waterfall of pop-up ads. As the ads will appear continuously, they will lead to a slower computer performance and frequent system crashes. Also, since they are so incredibly unreliable, they’ll also present you with a severe malware threat. So, ignore the pop-ups and avoid clicking on them no matter how enticing they seem! But the issues don’t stop there. The tool also places your personal and financial information in jeopardy as it spies on you. It keeps a thorough record of your every move until it determines it has collected enough data from you. Then, it sends it to the unknown third parties behind it, who can use it as they see fit. Are you going to allow that? Are you going to hand your private life to strangers with unclear intentions? Delete Mysearch123.com the first chance you get! You won’t regret it.
Attention! You should be aware that all of your accounts and passwords were likely compromised. Viruses are designed to collect every piece of private information. We advise you to change all your passwords, once you clean your computer, especially if you make online banking or shopping.
How Can I Remove Mysearch123.com Ads?
Compatible with Microsoft
SpyHunter is the recommended removal tool for Mysearch123.com Virus. You can use the free scanner to detect the parasite, however if you want to delete it automatically you need to register the antimalware program.
What if SpyHunter failed to Detect or Remove the infection? – Find out here how to use the FREE Support.
Remove Mysearch123.com infection Manually
If you perform exactly the steps below you should be able to remove the Mysearch123.com infection. Please, follow the procedures in the exact order. you may want to print this guide or look at it in another computer.
STEP 1: Remove Mysearch123.com from IE, Chrome or Firefox
STEP 2: Uninstall Mysearch123.com from your Add/Remove programs list
STEP 3: Delete Mysearch123.com Windows Registry Leftovers
STEP 1: Remove Mysearch123.com from IE, Chrome or Firefox
Mysearch123.com Ads will infect every browser you have. You need to do the steps one by one.
Remove From Internet Explorer
- Open Internet Explorer
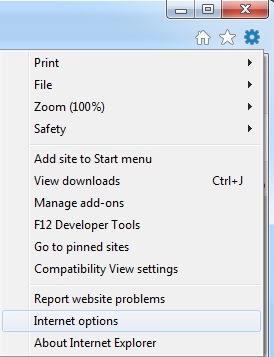
- Up to the Right Click on the Gear Icon
- Go to Toolbars and Extensions
- Disable any suspicious extension.
- If the button is not active, you need to go to your Windows Registry and delete the corresponding CLSID
- Then go back to the Gear Icon.
- Click on Internet options
- Select the Advanced tab and click on Reset.
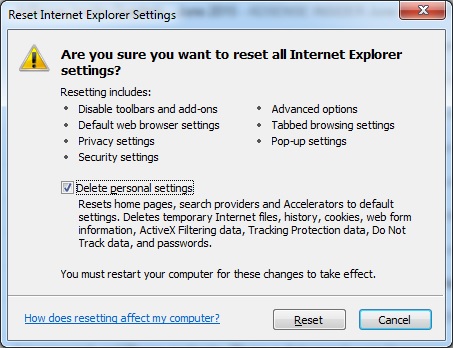
- Check the “Delete Personal Settings Tab” and then Reset
- Restart IE
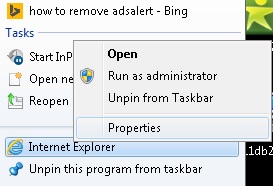
to make sure nothing is interfering with your browser, right click on the shortcut target and click properties
- In the target field you need to have the following command parameter: “C:\Program Files\Internet Explorer\iexplore.exe”
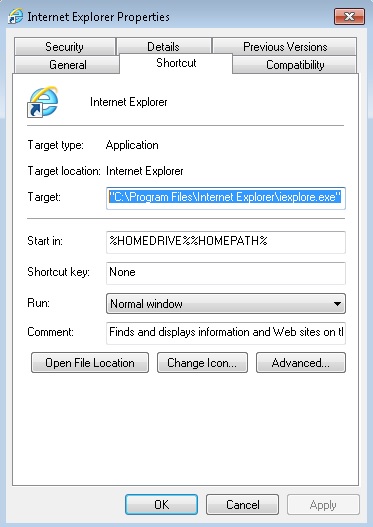
- if you have something else, just delete it and replace it.
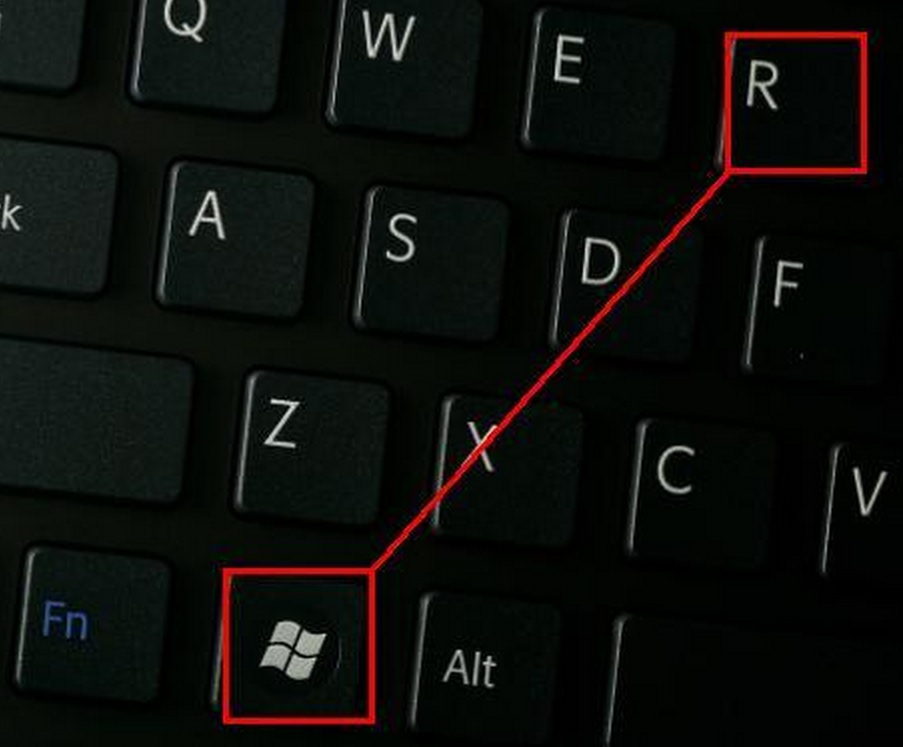
- simultaneously press the windows start button and “R”
- in the opened dialog box type “regedit“
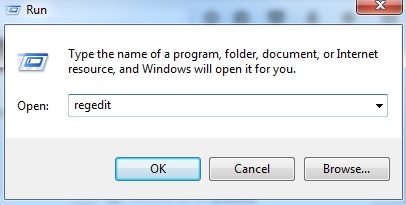
- Once the windows registry editor opens navigate to: HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main:Start Page
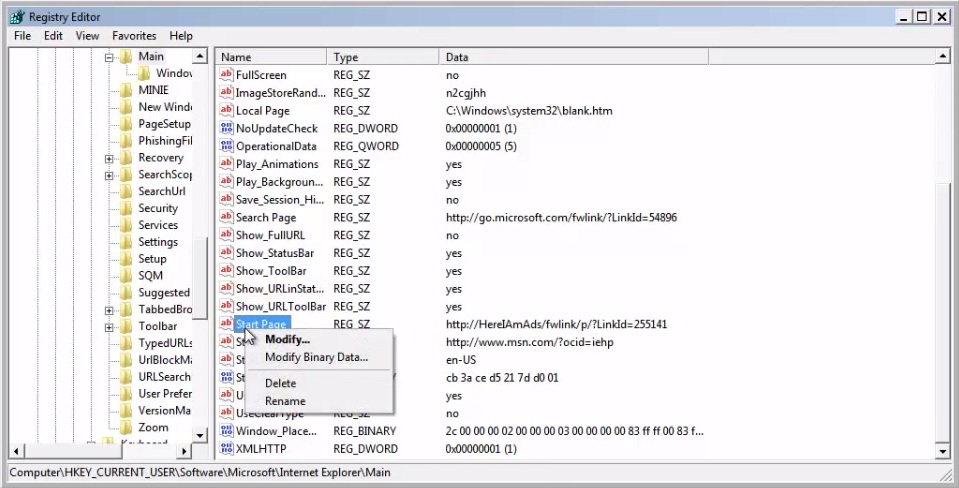 Modify the starting page with a value so that it corresponds to the webpage you want.
Modify the starting page with a value so that it corresponds to the webpage you want.- click OK and IE should be cleaned.
Remove from Mozilla Firefox
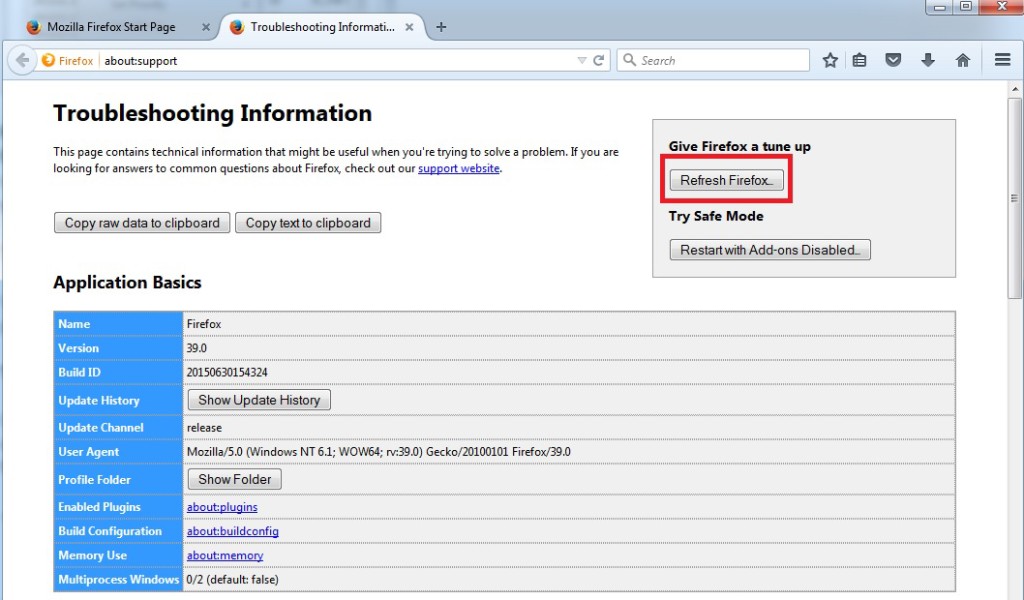
- Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Carefully review all add-ons and disable the unknowns
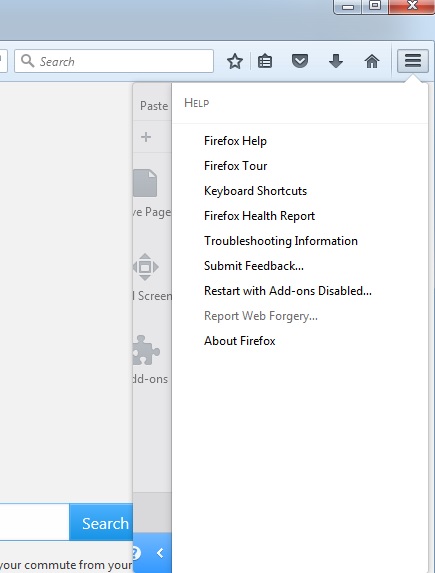
- Open the Firefox’s Help Menu
- Then Troubleshoot information
- Click on Refresh Firefox
Remove from Google Chrome
- Open Google Chrome
- On the upper right corner click the Chrome menu Icon (looks like three dashes)
- Hover Over More tools, then Extensions
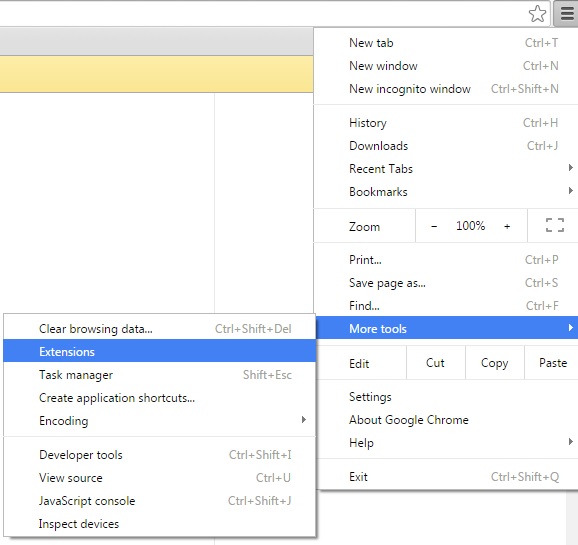
- in the extensions windows disable all unknown extensions
- On the upper right corner click the again the Chrome menu Icon (looks like three dashes)
- Click on Settings, Show Advanced Settings then Reset
STEP 2 : Uninstall Mysearch123.com from Your Computer
- Simultaneously press the Windows Logo Button and “R” to open the Run Command
- In the open dialog box type “Appwiz.cpl“
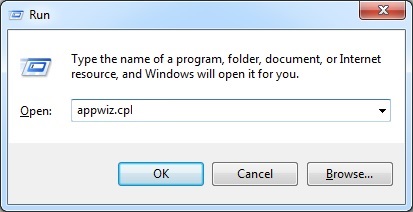
- Locate the Mysearch123.com program and click on uninstall/change.
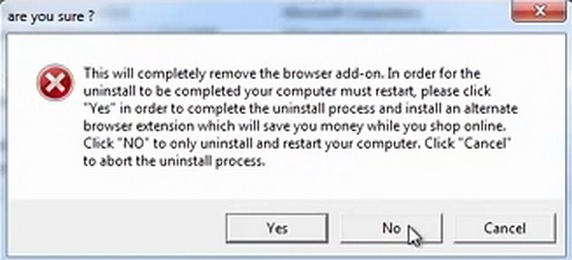
- Also, be warned that viruses always want to trick you into installing more crap. If you see a screen like this when you click Uninstall, Click NO!
STEP 3 : Delete Mysearch123.com Windows Registry Traces
These are the places in the windows registry where viruses inject their malicious payload. If you want to be 100% sure that nothing is hooking your system, check these locations. However, be very careful when editing the windows registry, because you can render your system unbootable.
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run
- HKLM \System\CurrentControlSet\Services
- HKLM \SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify
- HKLM \Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit
- HKCU\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\\Shell
- HKLM \Software\Microsoft\Windows NT\CurrentVersion\Winlogon\\Shell
- HKLM \Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKLM \Software\Microsoft\Windows\CurrentVersion\RunOnceEx
- HKCU\Software\Microsoft\Windows NT\CurrentVersion\Windows\load
- HKLM \Software\Microsoft\Windows NT\CurrentVersion\Windows
- HKLM \SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SharedTaskScheduler
Where HKCU stands for HKEY_CURRENT_USER
Where HKLM stands for HKEY_LOCAL_MACHINE
- Check these folders for corruption as well.
C:\Documents and Settings\All Users\Start Menu\Programs\Startup
C:\user\Profiles\All Users\Start Menu\Programs\Startup
C:\Documents and Settings\All Users\Start Menu\Programs\Startup